Center for Cooperative Research
Introduction
Objectives
Application
History of this project
What people are saying
Introduction
The Center for Cooperative Research seeks to encourage grassroots participation and collaboration in the documentation of the public historical record using an open-content model. New technology developed during the last decade has changed the nature of information production and distribution in two very important ways which are both fundamental to the Center’s objectives.
Firstly, new technology has decentralized the processes of information production and distribution, allowing the public to exert greater influence over the content and direction of the published historical record. Control of the production and distribution of information has slipped from the exclusive grip of large media conglomerates and is being appropriated at an increasingly fast pace by people at the grassroots level, whose previous lack of access to the means of information production and distribution prevented their ideas and knowledge from reaching the masses. This historically significant restructuring of the relationship between the producers and consumers of information is due to the fact that the dissemination of information to a large audience no longer requires large amounts of capital investment. Consequently, this process can no longer be easily monopolized, controlled, or filtered by a small elite group.
Secondly, Internet technology has created an environment where public collaboration in the production of information can take place at a level of efficiency comparable—if not superior—to that of the capital-intensive efforts of hierarchically-structured, private enterprises. This collaborative “open-content” model is politically and economically significant because it enables grassroots efforts to compete on a near equal footing with private industry while contributing to and enriching the intellectual commons.
Objectives
Reduce the fragmentation of the historical record
The Cooperative Research website seeks to help reduce the fragmentation of the historical record by connecting events whose temporal and spatial relationships are often obscured by a mass of contradicting and disconnected literature, the biases of the media, and the tendency for important past events to be relegated to the annals of forgotten history.
Increase the efficiency of information acquisition
Another objective of the Center is to increase the efficiency of research by reducing the tendency for researchers to duplicate the efforts of others. All too often, researchers—largely because of a fragmented historical record—needlessly spend a significant amount of time and energy bringing material together and establishing connections, even though this work may have already been performed by someone else. By collecting a mass of well-cited “event summaries” and “entity profiles” in a database, with descriptions about the relationships that exist among them, this website should reduce the frequency of such occurrences.
Increase the efficiency of information production
This project is premised on the notion that collaboration in an online “open-content” environment can greatly improve the efficiency and quality of information production in the public sphere as it allows contributors to build upon and improve the work of others in real time as part of a global community. Furthermore, products resulting from such arrangements are inherently more democratic than those of the private sector as they are created by a much broader spectrum of interests and perspectives.
Encourage the transition of oversight responsibilities from governments to civil society on a global scale.
The Center for Cooperative Research calls on people to abandon the widely-held assumption that governments can be relied upon to competently monitor the activities of themselves or the entities with which they have close relations. A major goal of this website is to encourage people to play an active role in scrutinizing the activities of all individuals, groups and institutions that wield significant political and economic power. Our position is that the power of oversight should not rest with governments, but with civil society itself.
Legal Templates
We also offer a wide selection of essential state-specific legal forms that may be customized for the most common legal procedures. One of the widely used legal documents is a bill of sale.
A Bill of sale Template verifies that a specific transaction took place and records all the essential details about the purchased item. A bill of sale serves as evidence and protects both parties of the deal. Usually, a bill of sale document includes such information as the buyer’s and seller’s contacts, description of the purchased item (it can be a car, boat, or aircraft), as-is clause (meaning that the buyer accepts the item’s condition at the time of sale), certificate of title, purchase price, and warranties (if any). These components are basic and vary depending on the type of bill of sale. It’s important not to confuse deed forms with bills of sale. Deed forms are usually used to transfer a title to real estate to the new owner either with or without consideration.
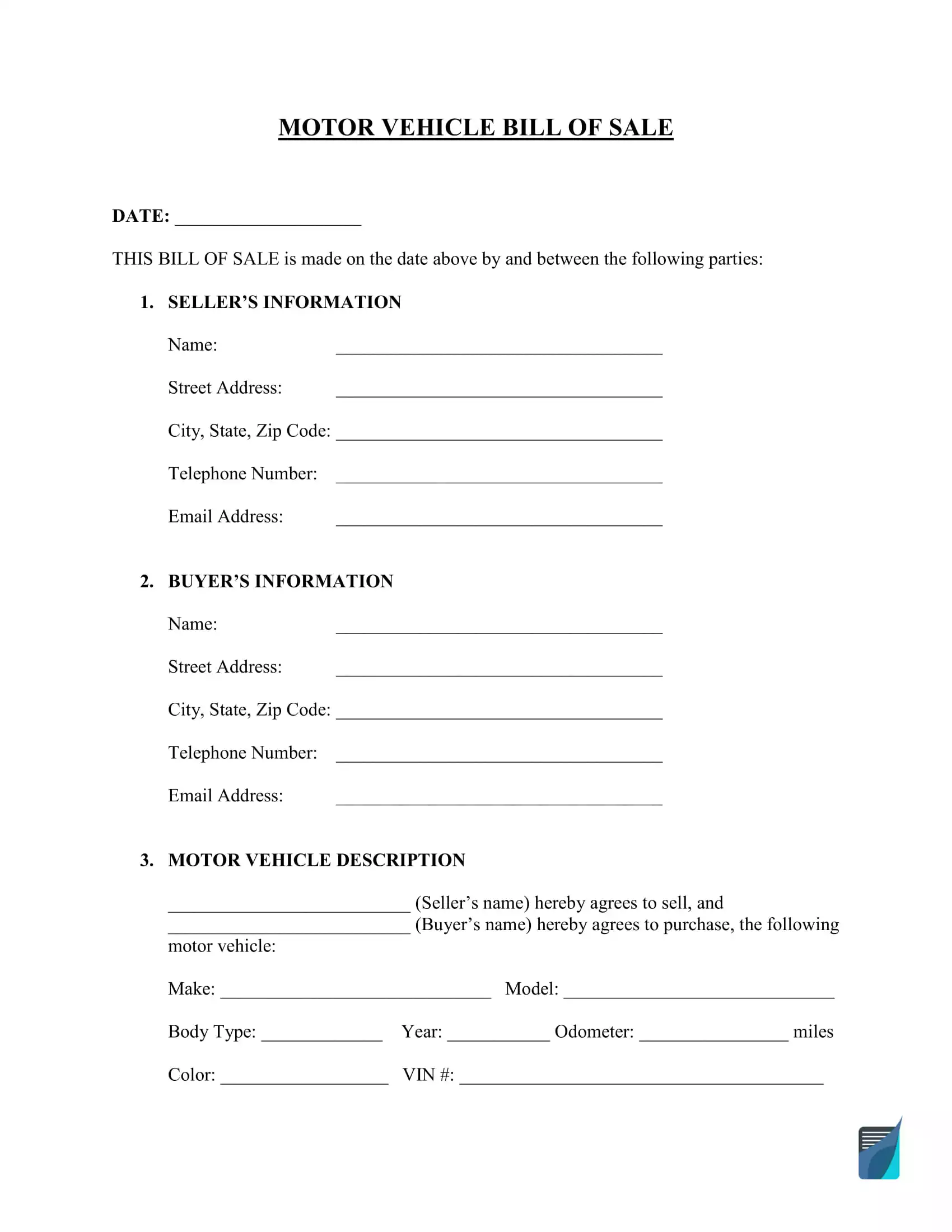
Selling or buying a car will require you to prepare a Vehicle Bill of Sale. Apart from basic details, the documents must contain the vehicle’s description, including vehicle identification number (VIN), its make, model, color, and year. It can also be required to attach an odometer statement and smog certificate. Many states require a bill of sale to register the purchased vehicle in the Department of Motor Vehicles (DMV).
If you want to sell or purchase a personal watercraft, you will have to sign a Boat Bill of Sale after the transaction. Although not required everywhere, it’s recommended to have one since it records all the details, including the boat description—model, year, length, hull identification number (HIN), and state registration number. If the boat has an outboard engine, the serial number of the motor should be given separately.
A Trailer Bill of Sale is used when you sell or buy any non-powered structure that can be hauled by another vehicle. Travel trailers and mobile homes are common examples of trailers. Although a trailer is a non-powered utility transport, it still has a vehicle identification number (VIN) that should be included in the bill of sale, as well as its make, model, and year of manufacturing. A trailer bill of sale will help you secure the transaction regardless of whether you’re selling or buying the transport.
Another essential bill of sale document is a Firearm Bill of Sale. Suppose you want to purchase a shotgun, rifle, or another type of firearm. In that case, you will need a record of such a transaction to protect yourself and avoid any future disputes or criminal issues related to the purchased item. A firearm bill of sale provides not only the gun description but also proof that the gun truly belongs to the seller and is not stolen.
Bill of Sale Templates by Type
Each specific occasion may need a specific bill of sale. For example, if you are going to sell or buy a piece of equipment, be ready to sign an equipment bill of sale. You are free to prepare an equipment bill of sale whenever you want. Still, this document should be used for valuable items such as office tools (projectors and computers) or household tools (lawnmowers and snowblowers). If you would like to buy a pet, you will find specific bills of sale, for example, a cat bill of sale or a bill of sale for a puppy. If you want to buy a motorcycle, be ready to sign a motorcycle bill of sale. So, check the list below and select an appropriate bill of sale type.
- Aircraft Bill of Sale
- Artwork Bill of Sale
- ATV Bill of Sale
- Bicycle Bill of Sale
- Business Bill of Sale
- Cat Bill of Sale
- Dirt Bike Bill of Sale
- Bill of Sale for a Puppy
- Equipment Bill of Sale
- Bill of Sale Furniture
- Generic Bill of Sale
- Golf Cart Bill of Sale
- Horse Bill of Sale
- Jet Ski Bill of Sale
- Livestock Bill of Sale
- Mobile Home Bill of Sale
- Moped Bill of Sale
- RV Bill of Sale
- Snowmobile Bill of Sale
- Tractor Bill of Sale
Sample Bill of Sale:
Bill of Sale Templates by State
The requirements for bills of sale may vary slightly by state. It’s especially relevant in terms of signing provisions. Usually, only the seller must sign the document. However, several states require that the buyers sign it as well. Similarly, most states do not require to sign a bill of sale in the presence of a notary public. But in such states as Louisiana, Nebraska, Maryland, New Hampshire, West Virginia, and Montana, a notary must witness both parties signing the document. Note that many states require that you sign a bill of sale when transferring autos, planes, boats, and similar assets.
If you are about to transfer ownership in Texas, you will need to prepare a Texas Bill of Sale. Boats and motor vehicles are the most regularly used Texas bills of sale as they are required to register these items. When registering a motor vehicle, you will have to fill out Texas Motor Vehicle Transfer Notification (Form VTR-346) along with your bill of sale and submit it to the Texas Department of Motor Vehicles within 30 days of the vehicle’s sale.
In Florida, you will need to sign a Florida Bill of Sale to register any motor vehicle or boat. To register these assets, your bills of sale must include such components as vehicle’s/boat’s make, model, year of manufacturing, color, and identification number. It must also provide the purchase price and transaction date. If you want to register the purchased gun, you won’t need to provide a firearm bill of sale. Still, it’s recommended to have one as it serves as your protection from any criminal issues regarding the gun.
A Missouri Bill of Sale serves as proof of ownership changes and is frequently required for various registrations. Thus, you will need a bill of sale to register your motor vehicle or personal watercraft. The document should provide all details regarding the seller, buyer, vehicle’s/boat’s description, date of the purchase, price, and parties’ signatures. When selling or buying a motor vehicle in Missouri, you will have to notarize your bill of sale.
Other state bill of sale templates you will find below:
- Alabama
- Alaska
- Arizona
- Arkansas
- California
- Colorado
- Connecticut
- Delaware
- Georgia
- Hawaii
- Idaho
- Illinois
- Indiana
- Iowa
- Kansas
- Kentucky
- Louisiana
- Maine
- Maryland
- Massachusetts
- Michigan
- Minnesota
- Mississippi
- Montana
- Nebraska
- Nevada
- New Hampshire
- New Jersey
- New Mexico
- New York
- North Carolina
- North Dakota
- Ohio
- Oklahoma
- Oregon
- Pennsylvania
- Rhode Island
- South Carolina
- South Dakota
- Tennessee
- Utah
- Vermont
- Virginia
- Washington State
- West Virginia
- Wisconsin
- Wyoming
State-specific Bill of Sale Templates by Type
A bill of sale is a written form that attests to a buyer’s property purchase from a seller. The document includes the contact information of the transacting parties, a description of the object sold, guarantees provided by the seller, restrictions related to the sale, the date of transfer, price, payment schedule(s), and the parties’ signatures. If you need a state bill of sale related to a specific type, we’ve covered you here as well. Below you will find state-specific templates divided by type.
Boat bill of sale forms by state
Boat bill of sale forms are important legal documents when selling or transferring ownership of a boat. This document provides evidence of the sale and should include the buyer and seller’s names and contact information, the date of sale, the boat’s make, model, hull identification number (HIN), and purchase price. The bill of sale should be signed by both parties and kept for their records. Here are some of the most popular boat bill of sale forms for different states:
- Boat Bill of Sale Alabama
- Arkansas Boat Bill of Sale
- Boat Bill of Sale Florida
- Boat Bill of Sale GA
- Kansas Boat Bill of Sale
- Louisiana Boat Bill of Sale
- Maryland DNR Boat Bill of Sale
- Boat Bill of Sale MA
- Boat Bill of Sale Michigan
- Boat Bill of Sale MN
- Mississippi Boat Bill of Sale
- Missouri Boat Bill of Sale
- NC Boat Bill of Sale
- Boat Bill of Sale Oregon
- SC Boat Bill of Sale
- Tennessee Boat Bill of Sale
- Texas Boat Bill of Sale
- Wisconsin Boat Bill of Sale
Firearm bill of sale forms by state
Firearm bill of sale forms are legal documents that transfer ownership of a firearm from one person to another. The bill of sale must be signed by both the buyer and the seller, and a licensed notary public must notarize it.
A firearm bill of sale form typically includes the following information:
-The names and contact information of the buyer and the seller
-A description of the firearm being sold, including the make, model, caliber, and serial number
-The date of the sale
-The purchase price of the firearm
-A statement that the seller is the legal owner of the firearm and that there are no outstanding liens or encumbrances on it
-A statement that the buyer is not prohibited by law from owning a firearm
-A statement that the buyer understands that it is their responsibility to comply with all applicable laws regarding the ownership and use of firearms
-Signatures of the buyer, the seller, and a witness
Here are some of the state-specific firearm bill of sale forms:
- Firearm Bill of Sale Alabama
- Arizona Firearm Bill of Sale
- Firearm Bill of Sale Florida
- Firearm Bill of Sale GA
- Firearm Bill of Sale Illinois
- Firearm Bill of Sale Indiana
- Louisiana Firearm Bill of Sale
- Missouri Firearm Bill of Sale
- Firearm Bill of Sale Nevada
- Firearm Bill of Sale Nc
- Firearm Bill of Sale Ohio
- Gun Bill of Sale SC
- Firearm Bill of Sale TN
- Texas Gun Bill of Sale
- Firearm Bill of Sale Utah
- Virginia Firearm Bill of Sale
Motor vehicle bill of sale forms by state
Motor vehicle bill of sale forms can be used to document the sale or transfer of a car, motorcycle, boat, or other vehicles.
The forms are typically simple, with space for the buyer and seller to fill in their personal information, as well as details about the vehicle being sold or transferred.
While a bill of sale is not required in all states, it can be a helpful way to protect both the buyer and seller in case there are any issues with the vehicle after the sale has been completed.
If you are selling or transferring a vehicle, be sure to check with your state’s DMV to see if a bill of sale is required and if there are any specific requirements that need to be included on the form.
Here are some of the vehicle bill of sale forms for specific states:
- Bill of Sale for Car Alabama
- Arizona Bill of Sale Car
- Arkansas Vehicle Bill of Sale
- CA DMV Bill of Sale
- Colorado Vehicle Bill of Sale
- CT DMV Bill of Sale
- Florida Vehicle Bill of Sale
- Georgia Vehicle Bill of Sale
- Idaho Vehicle Bill of Sale
- Bill of Sale For Car Illinois
- Vehicle Bill of Sale Indiana
- Iowa Vehicle Bill of Sale
- Kansas Vehicle Bill of Sale
- Louisiana Vehicle Bill of Sale
- Maine Vehicle Bill of Sale
- Maryland Vehicle Bill of Sale
- Massachusetts Vehicle Bill of Sale
- Michigan Vehicle Bill of Sale
- Missouri Vehicle Bill of Sale
- Montana Vehicle Bill of Sale
- Nebraska Vehicle Bill of Sale
- Nevada DMV Bill of Sale
- Bill of Sale Car NJ
- NM MVD Bill of Sale
- Bill of Sale for Car NY
- NC Bill of Sale For Car
- Ohio Vehicle Bill of Sale
- Oklahoma Vehicle Bill of Sale
- Oregon Vehicle Bill of Sale
- Vehicle Bill of Sale Pa
- SC Vehicle Bill of Sale
- SC DMV Bill of Sale
- Vehicle Bill of Sale TN
- Texas Vehicle Bill of Sale
- Utah Vehicle Bill of Sale
- Vermont Dmv Bill of Sale
- Virginia Vehicle Bill of Sale
- Washington State Vehicle Bill of Sale
- WV Dmv Bill of Sale
- Car Bill of Sale Wisconsin
Trailer bill of sale forms by state
Trailer bill of sale forms are documents that are typically used to transfer ownership of a trailer from one person to another. These forms can be obtained from a variety of sources, such as online websites or at your local department of motor vehicles office.
In most cases, a trailer bill of sale form will need to be filled out in order to complete the transaction. This form will usually require information such as the names and contact information of the buyer and seller, as well as a description of the trailer being sold.
It is important to make sure that all required information is included on the form before signing it. Once the form is signed, both parties will be legally bound by its contents.
Here are some of the state-spevific trailer bill of sale forms:
- Trailer Bill of Sale Arkansas
- Bill of Sale Trailer Colorado
- Trailer Bill of Sale Florida
- Trailer Bill of Sale GA
- NJ DMV Trailer Bill of Sale Form
- NY DMV Trailer Bill of Sale
- Trailer Bill of Sale NC
- Tennessee Bill of Sale for Trailer
- Trailer Bill of Sale Texas
Motorcycle bill of sale forms by state
Motorcycle bill of sale forms are very important if you are buying or selling a motorcycle. This document will list all of the necessary information about the transaction including the make and model of the motorcycle, the price, and the signatures of both parties. This form will protect both the buyer and the seller in case there are any problems with the bike in the future. Be sure to keep a copy of this form for your records. Here are some of the state-specific motorcycle bill of sale forms:
- Motorcycle Bill of Sale California
- Colorado Motorcycle Bill of Sale
- Florida Motorcycle Bill of Sale
- Motorcycle Bill of Sale Georgia
Application
The content of this website consists primarily of timelines and profiles of individuals, organizations, corporations and other entities. Each timeline consists of a collection of dynamically-generated “event summaries” which include the date the event took place, a summary of the event, and a link to its primary and/or secondary sources. At the end of each event summary, there is a list of all entities which actively participated in the event. Each of the participants listed at the bottom of the entry is linked to a profile page which includes a description of the entity’s relationships with other entities, a list of all quotes associated with the entity, as well as a timeline of all events in which the entity actively participated. Some event summaries also have an “additional info” link, which when clicked displays a list of quotes related to that event.
The editing and submission feature of the website is still being developed. Once implemented, visitors will be able to add new information and edit existing content online using html forms. Visitors will also be able to create their own timeline projects. Projects, which are basically just collections of timelines, can serve a variety of purposes. For example, a project can serve as a place in cyberspace where people collaborate in a grassroots investigation of a certain issue or it can simply be the work of one person interested in learning more about a topic. The timelines can be compiled from new or existing entries.
Each timeline will be exportable into xml so others can use or add to the data for their own applications or for posting on their own websites.
History of the Project
In late 2001, Derek Mitchell founded the Center for Cooperative Research with the specific aim of creating an online public forum where people could work together to document the historical record. His primary interest is in the development and promotion of systems—both technological and social—which decentralize the production and distribution of needed goods and services as a way to undermine the tendency for power and capital to become increasingly concentrated. He compiled the Iraq timeline and the Ousting of Aristide timeline in addition to the numerous outlines which were published on the earlier version of this website. He is a relatively recent graduate of James Madison University (1998, B. A. Anthropology).
In July 2002, freelance researcher Paul Thompson contributed his now-famous Complete 911 Timeline to the Cooperative Research website. His timeline is known far and wide and has had a major impact on public awareness with regard to the September 11 attacks on Washington and New York. The timeline is cited widely in the alternative media and was the major secondary source for several recent books including David Ray Griffin’s A New Pearl Harbour, a book referred to by historian Howard Zinn as “the most persuasive argument… for further investigation of the Bush administration’s relationship to that historic and troubling event.” Paul’s timeline was published as a book in September 2004.
More recently, in October 2003, Mike Bevin of Forgotten History joined the effort, developing the database application that now runs the Cooperative Research website. His website featured several timelines focusing on the numerous historical events that the US media and population have seemingly “forgotten.” These timelines now make up the History of US Interventions project.
On April 1, 2003, we launched the new dynamic version of the website. Ten months later, in mid-February 2005, we completed the beta version of the contribution system that allows people to add and edit timeline entries online.
Treatment of US troops
(1990s)
To save money, US Army officials order just 50 percent of the ALQ-156 flare-launching systems needed for the Illinois-Iowa National Guard fleet of Chinook helicopters. The flare-launching systems allow helicopters to evade heat-seeking missiles. “A conscious decision was made not to buy as many as we need,” Lt. Gen. Roger C. Schultz, director of the Army National Guard, later explains to the St. Louis Post-Dispatch. “It’s a decision that has some level of risk with it.”
1997
Major Clifford E. Day at the Air Command and Staff College in Alabama concludes in a paper that the US military’s reliance on soft-skinned Humvees during the operation in Mogadishu, Somalia “needlessly put… troops in harms way without the proper equipment to successfully complete the mission.”
(2003)
The Illinois-Iowa National Guard is deployed to Iraq. The unit is sent with 14 of its Chinook helicopters. However only two of them are outfitted with aircraft survivability equipment. The remaining helicopters will operate in Iraq unprotected.
(January 2003)
The Bush administration’s proposed 2004 defense budget would cap raises for E-1s, E-2s and O-1s at 2 percent, which is significantly below the average raise for military personnel of 4.1 percent.
March 2003 and later
US National Guard units deployed to Iraq are less well-equipped than their counterparts in the Army. Helicopters lack aircraft survivability equipment which allows the helicopters to evade enemy fire. Guardsmen complain of shortages of body armor, night vision goggles, ammunition, radar, uniforms, boots, cold weather gear, and two-way radios. Some guardsmen say that the equipment shortage are at times so severe that if they were operating according to Army rules the lack of equipment would have amounted to an “automatic mission-abort criteria.”
March 2003 and later
The US military sends 12,000 soft-skinned Humvees, some with canvas-skinned doors, to Iraq along with hundreds of transport vehicles which are equally unprepared for deployment in combat zones.
March 2003 and later
US military units in the Gulf, as well as those in the US preparing for deployment, contract local welders and steel fabricators to retrofit their light-armored vehicles with makeshift armor known as “Hillbilly,” or “Haji,” armor. [MSNBC, 4/15/2003; Daily Press, 9/26/2004; The Washington Post, 12/26/2003]
April 2003 and later
Roughly 44,000 US troops deployed to Iraq are provided with Vietnam-era Flak jackets instead of the modern Interceptor vests developed during the late 90s and in use since 2001. Flak Jackets do not protect troops from most of the ammunition types being used in Iraq. By contrast, the Interceptor vest—made of layered sheets of Kevlar with pockets in front and back for boron carbide ceramic plates—can stop high-velocity machine-gun bullets, shrapnel and other ordnance. They are also significantly lighter, giving troops more maneuverability when they need to respond quickly to threatening circumstances. Even in cases where troops are provided with the modern vests, they often lack the essential ceramic plates. [New York Daily News, 9/30/2003; Los Angeles Times, 10/02/2003; The Washington Post, 12/4/2003; Associated Press, 10/13/2003] Worried for the safety of their sons and daughters in Iraq, parents begin purchasing Interceptor vests and ceramic plates from body armor companies in the US and shipping them directly to their children’s units. Sometimes only the plates are available so soldiers improvise by taping the plates they have received from home to their Flak Jackets with duct tape—a practice that plate manufacturers say is unsafe.
May 27, 2003
US serviceman Mike Quinn is fatally shot at a traffic control point in Fallujah during an ambush. According to his friend, Staff Sgt. Dave Harris, he was killed because he wasn’t wearing his body armor. He had apparently given his vest to a young soldier who had not been provided with one of his own.
(Summer 2003)
Pentagon officials indicate that they will not ask Congress to renew a temporary increase in monthly Imminent-Danger Pay (IDP) (from $150 to $225) and Family-Separation Allowance (FSA) (from $100 to $250) to US soldiers stationed in combat zones. The temporary IDP and FSA increases, which were put into effect retroactively in April, are set to expire on September 30. In August, when a journalist asks the White House about its views on the plan not to renew the pay increases, a spokesperson refers the reporter to a June Pentagon budget report which warned that the DoD budget can’t sustain the higher payments. [The Army Times, 6/30/2003; San Francisco Chronicle, 8/14/2003] But after the planned rollback of the benefits becomes a public controversy, the Pentagon issues a statement on August 14 saying that it intends to ensure that those serving in Iraq and Afghanistan “continue to receive this compensation at least at the current levels.” The statement says nothing about troops deployed on dangerous missions in other regions.
(June 2003)
The White House complains that certain pay-and-benefits incentives for US soldiers that Congress added to the 2004 defense budget are wasteful and unnecessary—including a proposal to double the $6,000 gratuity paid to the families of soldiers who are killed in action.
(Summer 2003-March 2004)
The US Army’s official guidance on the issue of “hardening” soft-skinned Humvees and other lightly-armored vehicles includes a recommendation for soldiers to put sandbags on the floorboards to reduce the impact of explosions. Since the summer, the soldiers’ preferred solution to the problem of unprotected vehicles has been to hire local contractors to add steel to the bodies of their vehicles (see March 2003 and later).
September 25, 2003
Department of Defense officials ask Congress not to renew a temporary increase in the Family Separation Allowance (FSA) and Imminent Danger Pay (IDP) for deployed forces that had been enacted in April. Instead, Defense suggests raising the Hardship Duty Pay for troops deployed only in Iraq and Afghanistan. David Chu, the department’s top personnel official, says that the April raises were like “using a sledgehammer to hit a small nail.” The Pentagon’s intent to rollback the FSA and IDP reignites a controversy that had sprung up during the summer (see (Summer 2003)) when it was first revealed that the White House supported the Defense Department’s plan to save money by cutting back on the two programs. [Stars and Stripes, 10/4/2003] The final National Defense Authorization bill, which is passed by Congress in November, rejects the Pentagon’s recommendations and renews the pay increases.
October 2003
Approximately 600 sick or injured members of the US Army Reserves and National Guard are in “medical hold” at Fort Stewart where they are kept “in rows of spare, steamy and dark cement barracks in a sandy field” while doctors review their cases to determine how sick or disabled they are and whether or not they are eligible to receive benefits. Many of the soldiers in medical hold complain that they have been languishing there for “months” and that the conditions are “substandard.” Some soldiers also claim that the Army is trying to refuse them benefits on grounds that their injuries and illnesses are due to a pre-existing condition. Willie Buckels, a truck master with the 296th Transportation Company, explains to UPI reporter Mark Benjamin how he feels about the Army’s treatment of the soldiers: “Now my whole idea about the US Army has changed. I am treated like a third-class citizen.” [The Coastal Courier, 10/22/2003; CNN, 10/19/2003; United Press International, 10/20/2003; United Press International, 10/17/2003]
October 2003
More than 18 months after the US began its ground invasion of Iraq, US troops are still waiting for the Army to retrofit their supply trucks.
October 2003
Army Pfc. John D. Hart telephones his parents in Bedford, Massachusetts and complains that he feels unsafe patrolling in his company’s unprotected soft-skinned Humvees which do not have bulletproof shielding or even metal doors. A week later, the 20-year-old paratrooper and another soldier, David R. Bernstein, are killed when their vehicle is hit with small-arms fire and rocket-propelled grenades in Taza outside the northern city of Kirkuk. The driver of the vehicle, Specialist Joshua Sams, will later explain to the Boston Globe that Bernstein had bled to death after being struck by a bullet that ripped through the Humvee.
October 2003
Acting Secretary of the Army Les Brownlee claims that the Army has ordered as many “up-armored” vehicles as its contractors can produce, but says that they will not be ready until mid-2005. But Brian T. Hart, whose 20 year old son was killed in a soft-skinned Humvee (see October 2003), investigates the secretary’s claim and learns that the armor manufacturers are not at full production. He takes this information to Senator Edward M. Kennedy who then helps him pressure the Army to speed up production and move the date that they will be available up to January.
January 16, 2004
The Department of Veterans Affairs announces that it is immediately cutting health care benefits to Category 8 veterans. The agency says that the decision to cut the benefits, which will affect an estimated 164,000 US veterans, is made because there is a growing backlog of veterans still waiting to receive their first treatment from a VA health care facility. Veterans classified as Category 8 are veterans who do not suffer from military service-related disabilities or health problems and who make $30,000 to $35,000 or more per year.
June 2, 2004
The US Army announces the extension of its “stop-loss” program which means that thousands of soldiers scheduled to retire or otherwise leave the military will be required to stay in Iraq for the remainder of their unit’s deployment. [Associated Press, 6/2/2004] Critics call the policy a “backdoor draft.”
June 13, 2004
Spc. Eric McKinley from the Oregon National Guard is killed when his unarmored Humvee hits an Improvised Explosive Device (IED) outside of Baghdad. Also in the vehicle is fellow guardsman Staff Sgt. Sean Davis who suffers shrapnel wounds and burns. The Humvee had been fitted with plywood, sandbags, and armor salvaged from old Iraqi tanks. McKinley was supposed to have been discharged from the Oregon National Guard a few months before, but he was kept in Iraq because of the Army’s “stop-loss” policy (see June 2, 2004).
(Late October 2004)
Oregon national guardsman Sean Davis tells CBS 60 Minutes that his unit was not provided with enough ammunition when they were deployed to Iraq and that the guardsmen lacked night vision goggles and two-way radios. He explains they used walkie-talkies that they or their families purchased on their own. “And anybody can pick up those signals, you know,” he notes.
(Late October 2004)
US Representative David Obey, a senior Democrat on the House Appropriations Committee, proposes to reduce Bush’s recent tax cuts for the roughly 200,000 Americans who earn more than $1 million a year in order to help offset the $1.5 billion cut in Bush’s military construction budget. By reducing the tax break from $88,300 to $83,500 the government would be able to restore $1 billion to the budget. But the Republican majority on the construction appropriations panel immediately shoots down Obey’s proposal.
December 2004
Upon being released from Fort Hood, Texas, 27-year-old Spc. Robert Loria is presented with a $1,768.81 bill from the US Army. Loria was seriously injured on February 9, when the Humvee in which he was riding was hit by a roadside bomb. [Philadelphia Inquirer, 3/21/2004] The explosion “tore Loria’s left hand and forearm off, split his femur in two and shot shrapnel through the left side of his body.” [Times Herald Record, 12/10/2004 [a]] After four months of rehabilitation at Walter Reed Hospital in Washington, D.C., he was sent to Fort Hood where he stayed several more months. When he is finally ready to leave, instead of receiving a check for the $4,486 he thought was owed to him, he receives a huge bill. The Army says he owes $2,408.33 for 10 months of family separation pay that the Army mistakenly paid him, $2,204.25 in travel expenses from Fort Hood back to Walter Reed for a follow-up visit, and $310 for unreturned equipment that Loria says was damaged or destroyed when his Humvee was attacked. Including taxes, the total amount Lori owes the Army is $6,255.50, almost two thousand more than the amount he thought was owed to him. After a local newspaper runs a story on his situation and causes a public uproar, the Army waives most of Loria’s debts.
What people are saying about the Center for Cooperative Research
From the acknowledgements of House of Bush, House of Saud by Craig Unger
“The Center for Cooperative Research is another valuable Internet tool. Because I made a practice of citing original sources, it does not appear in my notes nearly as often as it might. However, its timelines about 911 and related issues often helped me find exactly what I was looking for. I highly recommend it to anyone doing research on 9/11 and I encourage its support.”
From the acknowledgements of Cover-Up by Peter Lance
“As mentioned throughout, I was blessed in this state of my research with access to Paul Thompson’s remarkable timelines from the Center for Cooperative Research each citation in that database is supported by a news story from the mainstream media. … Any research, reporter, or scholar with an interest in the war on terror would consider the Cooperative Research timelines a bonanza of open source information.”
From the acknowledgements of 911 Commission Report: Omissions and Distortions by David Ray Griffin.
“[M]y greatest dependence was on Paul Thompson’s timeline … [at the Center for Cooperative Research’s website]”
Visitors to the Center for Cooperative Research website.
“This site is so brilliant. Thank you for doing it!” – Suzanne DeBolt
“Your organization and your Web site truly realize the potential of the Internet for collaborative study, research, and understanding. This is one of the best, if not the best, resource on the Web for detailed, unbiased, and unfiltered analysis of recent events.” – Peter Orvetti
“… absolutely brilliant website, of great value to all! Splendid work.” – Nigel
“I just want to let all of you know what an absolutely amazing website cooperative research is. It has been the most informative site I have come across and I tell EVERYONE about it. I can not even begin to imagine the time and effort put into making this site what it is, and it amazes me how much it has grown over the past year (after finding it while doing research for an English paper for college.) Keep up the outstanding work, I can speak for many people when I say it is appreciated and making a difference.” – Amanda Rae
“…yours is the very best site I have found. And you gave me hope when it was hard to come by.” – Kathryn Welch, Blacksburg, VA
“I consider your project as one of the most important web-based projects aimed at combating what I call political amnesia.” – Morten Nielsen